Ensure Your Industrial Operations and Security Infrastructure Are Operating As Intended
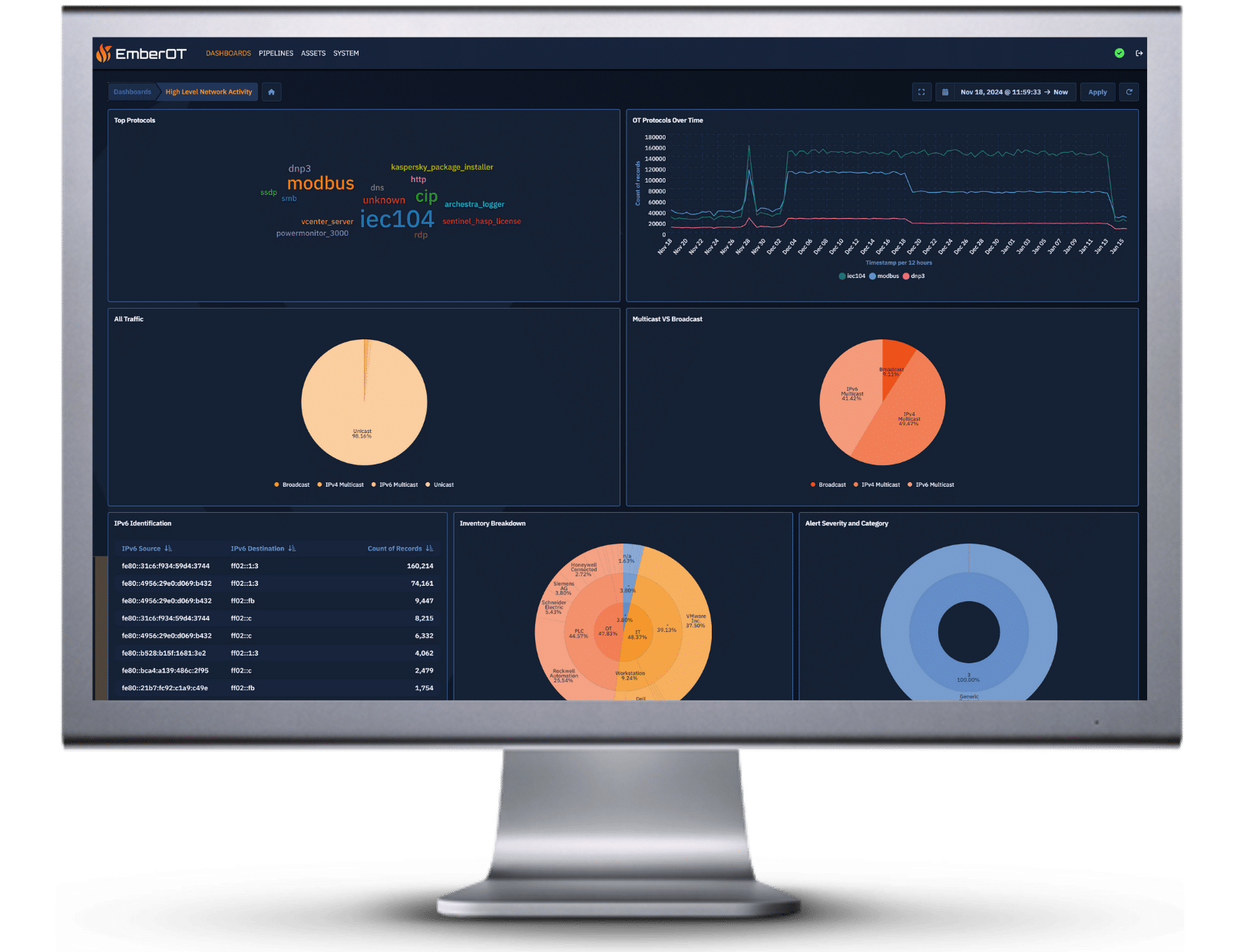
Hidden gaps in asset inventories, outdated controls, and unoptimized security measures can undermine your operations. EmberOT’s Firewatch Assessment harnesses our advanced Ember sensors and deep industry expertise to perform a comprehensive health check of your OT environment. We illuminate every corner, from remote field devices to your core control systems, ensuring your assets are current and your controls are working as intended.